Secure IT Infrastructure 473588361 Online

A secure IT infrastructure is essential for businesses in the digital landscape. It protects sensitive data from evolving cyber threats. Implementing best practices, such as strong password protocols and multi-factor authentication, is critical. Organizations must also utilize advanced security tools to bolster their defenses. However, despite these measures, vulnerabilities can still persist. This raises the question of how companies can develop a robust cybersecurity strategy that withstands potential breaches.
Understanding the Importance of Secure IT Infrastructure
Although organizations increasingly rely on digital systems for operational efficiency, the necessity of a secure IT infrastructure cannot be overstated.
Effective data protection hinges on robust network security measures that safeguard sensitive information from cyber threats.
A well-architected infrastructure not only mitigates risks but also empowers organizations to operate freely, fostering innovation while maintaining trust among stakeholders through comprehensive security protocols and contingency plans.
Essential Best Practices for Online Security
Numerous best practices exist to enhance online security, each contributing to a more resilient IT infrastructure.
Effective password management is crucial, employing complex and unique passwords for different accounts.
Additionally, fostering phishing awareness among users can significantly mitigate risks associated with deceptive emails and links.
Implementing these practices not only safeguards sensitive information but also empowers individuals to navigate the digital landscape with confidence.
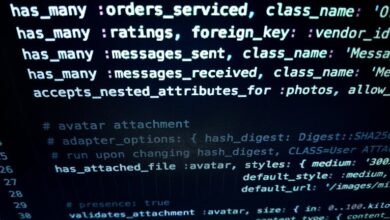
Tools and Technologies to Fortify Your IT Systems
In addition to best practices for online security, employing the right tools and technologies is imperative for fortifying IT systems against evolving cyber threats.
Cloud security solutions enable robust data protection by leveraging encryption and access controls.
Additionally, network segmentation reduces attack surfaces, isolating sensitive systems and limiting lateral movement.
Together, these strategies enhance resilience, ensuring a more secure IT environment for organizations seeking autonomy and protection.
Developing a Resilient Cybersecurity Strategy
A comprehensive cybersecurity strategy is essential for organizations aiming to withstand the relentless evolution of cyber threats.
Implementing robust cyber threat modeling enables proactive identification of vulnerabilities, while a well-defined incident response plan ensures swift recovery from breaches.
Conclusion
In conclusion, a secure IT infrastructure is paramount for safeguarding sensitive data in an increasingly digital landscape. Notably, a recent study revealed that 60% of small businesses that experience a cyberattack go out of business within six months. This statistic underscores the critical need for organizations to adopt best practices, leverage advanced security tools, and develop robust cybersecurity strategies. By prioritizing security, businesses can protect their digital assets, foster stakeholder trust, and ensure long-term operational resilience.