Secure IT Infrastructure 120839046 Online

A secure IT infrastructure is critical in today’s digital landscape. It combines various elements like network security, data encryption, and continuous monitoring to safeguard digital assets. Organizations must also recognize common vulnerabilities that can compromise their systems. Additionally, adherence to compliance and regulatory requirements is vital. Each of these aspects plays a significant role. Understanding their interconnectivity can reveal deeper insights into maintaining robust security measures. What strategies can organizations adopt to enhance their defenses?
Understanding Secure IT Infrastructure: Key Components
A secure IT infrastructure comprises several critical components that collectively safeguard an organization’s digital assets.
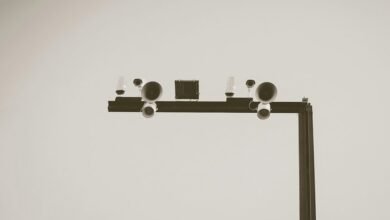
Network security establishes protective measures against unauthorized access, while data encryption ensures that sensitive information remains confidential during transmission and storage.
Together, these elements form a robust defense strategy, empowering organizations to maintain operational integrity and protect individual freedoms, which are essential in today’s digital landscape.
Identifying Common Vulnerabilities in Online Systems?
How can organizations effectively identify vulnerabilities within their online systems? Conducting a thorough vulnerability assessment and employing threat modeling techniques are essential steps.
Vulnerability assessments systematically examine systems for weaknesses, while threat modeling anticipates potential attack vectors.
Best Practices for Strengthening Your IT Security
Numerous best practices exist for strengthening IT security, providing organizations with a structured approach to mitigate risks.
Implementing comprehensive employee training enhances awareness of potential threats, fostering a culture of vigilance.
Additionally, leveraging threat intelligence equips organizations with timely information on emerging risks, enabling proactive defenses.
Together, these strategies create a robust framework that not only protects assets but also promotes organizational freedom and resilience.
Navigating Compliance and Regulatory Requirements
Compliance and regulatory requirements significantly influence the landscape of IT security. Organizations must navigate various compliance frameworks to ensure adherence, fostering trust and integrity.
Regulatory audits serve as critical checkpoints, assessing conformity and identifying vulnerabilities. By prioritizing these frameworks, businesses not only mitigate risks but also enhance their operational freedom, enabling them to innovate while maintaining a robust security posture in a complex regulatory environment.
Conclusion
In conclusion, a secure IT infrastructure acts as a fortress, defending against the relentless tide of cyber threats. By understanding its key components, recognizing vulnerabilities, and adopting best practices, organizations can not only safeguard their digital assets but also navigate the complex landscape of compliance and regulatory requirements. As the digital realm continues to evolve, fostering a culture of security awareness among employees will be paramount in ensuring resilience and maintaining the trust of stakeholders.